DDoS stands for distributed denial-of-service. This type of cyberattack is a malicious attempt to disrupt traffic to a targeted server or network by overwhelming it with a flood of internet traffic. A DDoS attack is like a highly unexpected traffic jam on the highway that prevents normal traffic from reaching its destination. These attacks are effective when multiple computer systems or IoT devices are compromised. Moving forward with the traffic jam comparison, imagine a car in each lane of a highway slamming on their brakes at the same time. The more IoT devices (or cars) that are compromised, the more successful the attack.
How do DDoS attacks work?
DDoS attacks are carried out by networks of computers or IoT devices that have been infected with malware. Malware is any type of software that has malicious intent: ransomware, trojans, viruses, worms, or any other type of intentionally harmful software. Business networks are comprised of countless internet connected devices that can potentially be infected with malware. Attackers will generally compromise as many devices on the network as possible before taking control of them remotely. 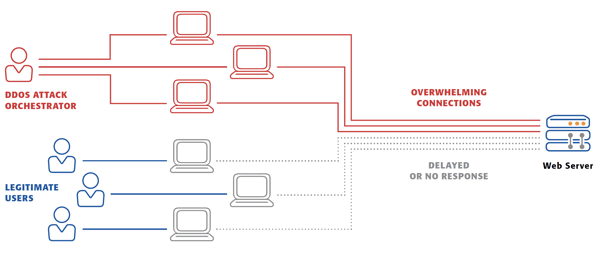
An individual compromised device is referred to as a “bot” and a network of compromised devices is a “botnet.” Once the botnet is established, the hacker can send instructions to each bot to target a server or IP address causing it to be overwhelmed, resulting in a denial-of-service. Since these devices are recognized by the servers, it can be difficult for them to decipher “normal” traffic from attack traffic.
How do you identify a DDoS attack?
There are a few different signs that your network is suffering from a DDoS attack, the most obvious being that a site or service becomes slow or unavailable. Since there are many reasons why a site or service may become unresponsive it is important to investigate each instance further. Traffic analytics and mitigation tools exist to help identify these attacks quickly before any damage or downtime is caused. While there are many different signs of a DDoS attack, some of the most common include:
- A sudden surge of requests received to a single webpage or endpoint of a service
- A flood of traffic coming from users sharing a similar behavioral profile like geographic location, web browser, or device type
- Traffic spikes at odd hours or at abnormal intervals (once every minute for example)
- Suspicious levels of traffic originating from on IP address or an IP address range
DDoS Mitigation
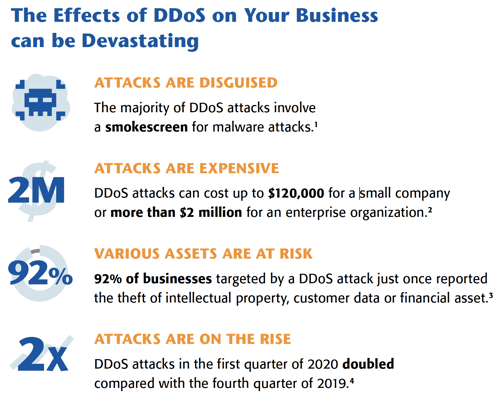
As we mentioned previously, there are mitigation tools and traffic analytics available that can take the pressure off your IT team and ensure that your business is protected from DDoS attacks. These attacks can happen to small companies as well as large enterprises and they are extremely costly. Our partner, Consolidated Communications offers top-notch DDoS mitigation solutions. They help many of our customers identify and prevent DDoS attacks every single day. They are reputable and proactively identify new or up-and-coming attack methods, so you’re IT team can focus on your business needs.
If you have any questions about DDoS attacks or DDoS Mitigation, please reach out to us at ContactUs@Matrix-NDI.com or call 763-475-5500.
*All graphics in this blog post are courtesy of Consolidated Communications

