DDoS stands for distributed denial of service which is where a malicious attempt is made to disrupt normal traffic to a targeted server, network, or service by overwhelming it with a flood of internet traffic. DDoS mitigation is the process of protecting the targeted server or network from this type of attack. From a high level, DDoS mitigation is defined by four different stages:
Detection
Detection is where deviations in traffic flow are detected. The DDoS mitigation solution understands what normal traffic looks like for your business, and continuously monitors for any abnormalities. The goal is instantaneous detection.
Diversion
Diversion is where the detected abnormal traffic is rerouted away from the target by either DNS (domain name system) or BGP (border gate protocol) routing. From there the system makes a choice to either filter or discard the traffic completely.
Filtering
The filtering stage is where DDoS traffic is weeded out. The mitigation system identifies patterns and looks at differences between legitimate traffic and malicious visitors. The goal of this stage is to block any attacks without interfering with the user experience.
Analysis
Analysis is where the system logs any attack or event to both identify the attacker and improve future functionality. There are different levels of analysis available. Standard logging will require some manual investigation, but there are advanced security analytic tools available that can offer more granular insight into an attack to understand how it happened and potentially where it came from.
What to consider when choosing a DDoS Mitigation provider
Every business is unique and has different priorities when it comes to choosing a provider. There are a few key aspects to keep in mind as you research and ultimately decide on the best solution for you.
Network Capacity
Network capacity is one of the major ways of understanding the strength of a DDoS mitigation solution. This reflects the amount protection available to you when an attack occurs. An example of this would be a 1 Tbps (terabit per second) theoretically being able to handle the same volume of attack traffic. There is a certain amount of bandwidth required for the service to maintain its baseline functionality to consider as well. You will want to ensure that the network capacity of the mitigation tool is high enough to cover the amount of traffic you generally receive to your network.
Processing Capacity
Processing capability is represented by forwarding rates which is measured in Mpps (millions of packets per second). Understanding the processing power of the tool is paramount to understanding how strong the defense will be during an attack. If you think of DDoS mitigation as a wall, the processing power is how thick the wall is and how hard an attack is can withstand before it crumbles. In today’s world it is common for attacks to reach 50 Mpps, but sophisticated attacks can reach between 200-300 Mpps.
Time to Mitigation
Time to mitigation is rather self-explanatory but you should always ask a provider what their stats are. Once an attack has been detected, how long does it take for mitigation to occur? DDoS attacks can take down a targeted server or network within minutes, resulting in a recovery process of multiple hours. The impact of this downtime can be extremely costly to businesses and potentially impact operations for weeks or months.
Network Layer vs Application Layer Mitigation
Network Layer DDoS attacks focus on volume and rely on large scale traffic to cause a great deal on your IT infrastructure. There are a few different methods of mitigating this type of attack including null routing, sinkholing, scrubbing, and IP masking. The goal of both methods is to separate legitimate traffic from malicious traffic.
Application Layer DDoS attacks are usually on a smaller scale than Network Layer attacks, but they are much more covert. This type of attack attempts to mimic normal traffic to evade security tools. To stop Application Layer attacks your solution will need to be able to profile HTTP/S traffic and be able to decipher between bots and legitimate users.
Pricing
There are a few different pricing models on the market for DDoS mitigation. One pricing model isn’t necessarily better than the other as it comes down to preference. “Pay as you go” pricing is where you don’t pay anything unless you are attacked. This can be attractive to businesses since there is no fee up front, but it can be very costly if you do have an attack. This pricing model is a gamble, so be sure you understand the terms before you choose this route.
Service-based pricing is where there is a base price for the DDoS mitigation solution with special pricing for implementation, support, or other add-ons. This solution may work well for your team if you have a well-versed IT team that can do the implementation and analysis, but it can become costly if you need support from the provider.
A flat monthly fee is the most simple and common pricing model for DDoS mitigation. With this type of pricing the solution provider should be very hands on from implementation through the analytic phase of an attack.
How to Choose a DDoS Mitigation Provider
As you can see, there are a lot of factors that go into choosing the best provider for DDoS mitigation. Our goal here was to help you gain some insight into questions to ask potential providers before you make a selection. We partner with Consolidated Communications, a top-of-the-line DDoS Mitigation provider, and we always recommend working with them for protection against these types of attacks. We work closely with them to ensure our customers receive the support, solution, and pricing model that will work best for their unique business.
If you have any questions about DDoS Mitigation solutions, reach out to us at ContactUs@Matrix-NDI.com or call 763-475-5500.
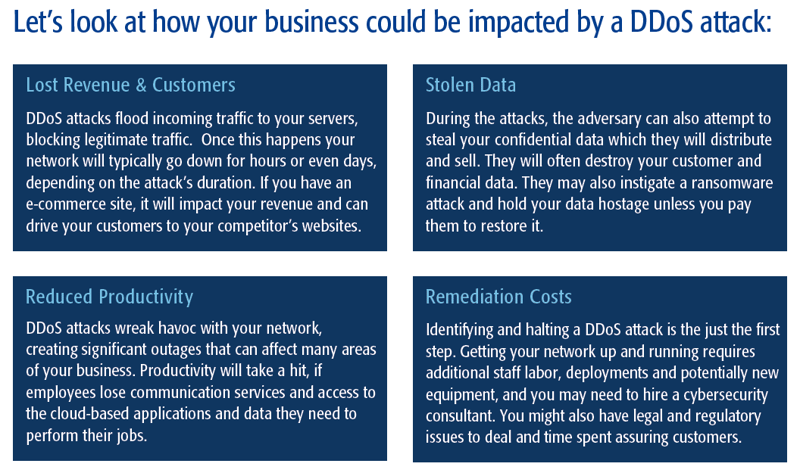
*DDoS Impact graphic courtesy of Consolidated Communiciations

