UCaaS or Unified Communications as a Service is an efficient, cost effective, and scalable form of business communication that has become more common than traditional phone systems. As remote work and hybrid models increase in popularity, mobile enabled voice applications and video conferencing are paramount for efficient business operations.
While we know that some UCaaS platforms are better than others when it comes to uptime, cost, and functionality – security is something that should be at the front of mind when selecting an option for your business.
Here we are going to discuss end-to-end encryption (E2EE), how it differs from point-to-point (P2P) encryption, and what it means regarding UCaaS.
What is end-to-end encryption?
The simplest explanation of end-to-end encryption (E2EE) is that only the endpoints can access the data. The endpoints are the sender and the receiver of the message, voicemail, file, or video conference. All data sent from one point to another passes through a server(s) and without E2EE the server(s) can see and read the data being sent. The more points in the journey that the data is unencrypted, the more potential for unwanted access there is.
You can think of this as if your data is a package traveling down a hallway with other people and packages. E2EE would be a padlock on this package that only you (the sender) and the receiver have the unique key to.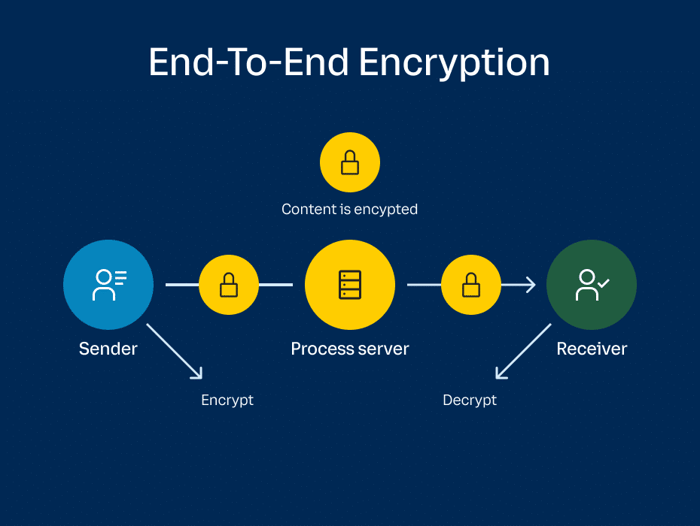
What is point-to-point encryption?
Point-to-point encryption is a standard protocol that is usually referenced when talking about credit card payment transactions, meaning a card reader sends an encrypted transaction request to a processing system and is either approved or denied. In this case we are looking at it from a data-in-transition perspective with a focus on video conferencing or voice.
In this context you (the sender) join a video conference with one or more other people. The data you are sending is received by the video provider’s (the tool you are using) processing server, which will decrypt the data before re-encrypting it and passing it along to the end user you are trying to communicate with. This means that for a moment your communication is unencrypted. While this doesn’t necessarily mean it is vulnerable, it just means that it is decrypted during its journey to the receiving user.
*photo from RingCentral.com
How does end-to-end encryption benefit UCaaS users?
If you discuss confidential or sensitive information through video conferencing or cloud-based voice platforms, E2EE allows for total privacy since it is only decrypted by the person designated to receive it. It adds an extra level of security since there could be eavesdroppers or bad actors if a provider’s processing server is compromised. To put it simply, E2EE ensures that the contents of your conversations are confidential, even if you are utilizing a public internet network.
Is there a downside to end-to-end encryption for UCaaS?
The main downside to E2EE when using a UCaaS solution is that the provider cannot offer meeting or video recording, live transcripts, or virtual backgrounds. These services are provided by the provider’s processing server so when you remove that server’s ability to decrypt your data, you remove its ability to record, transcribe, or include fun backgrounds.
Major UCaaS providers, such as RingCentral, are working on making these features possible with E2EE through client-side processing, so stay tuned!
Which option is best for you?
The beauty of UCaaS solutions that offer E2EE is that you can turn the feature on and off if you would like to. With RingCentral, if you have a meeting or training that you would like to have recorded you can turn it off, and if you are having a confidential conversation, it can be turned on by checking a box. So, the answer is that it really depends on your business and the level of confidentiality you require.
If you would like to learn more about RingCentral, other UCaaS solutions, or end-to-end encryption reach out to us at ContactUs@Matrix-NDI.com or call 763-475-5500.

